In today’s digital-first communication landscape, SMS remains one of the most trusted and high-engagement channels for businesses. However, with this trust comes risk. DLT header misuse has emerged as a growing concern, exposing businesses and customers to fraud, phishing attacks, and reputational damage.
If you rely on SMS for customer communication, understanding SMS
header fraud and brand spoofing in SMS is no longer optional- it’s
essential.
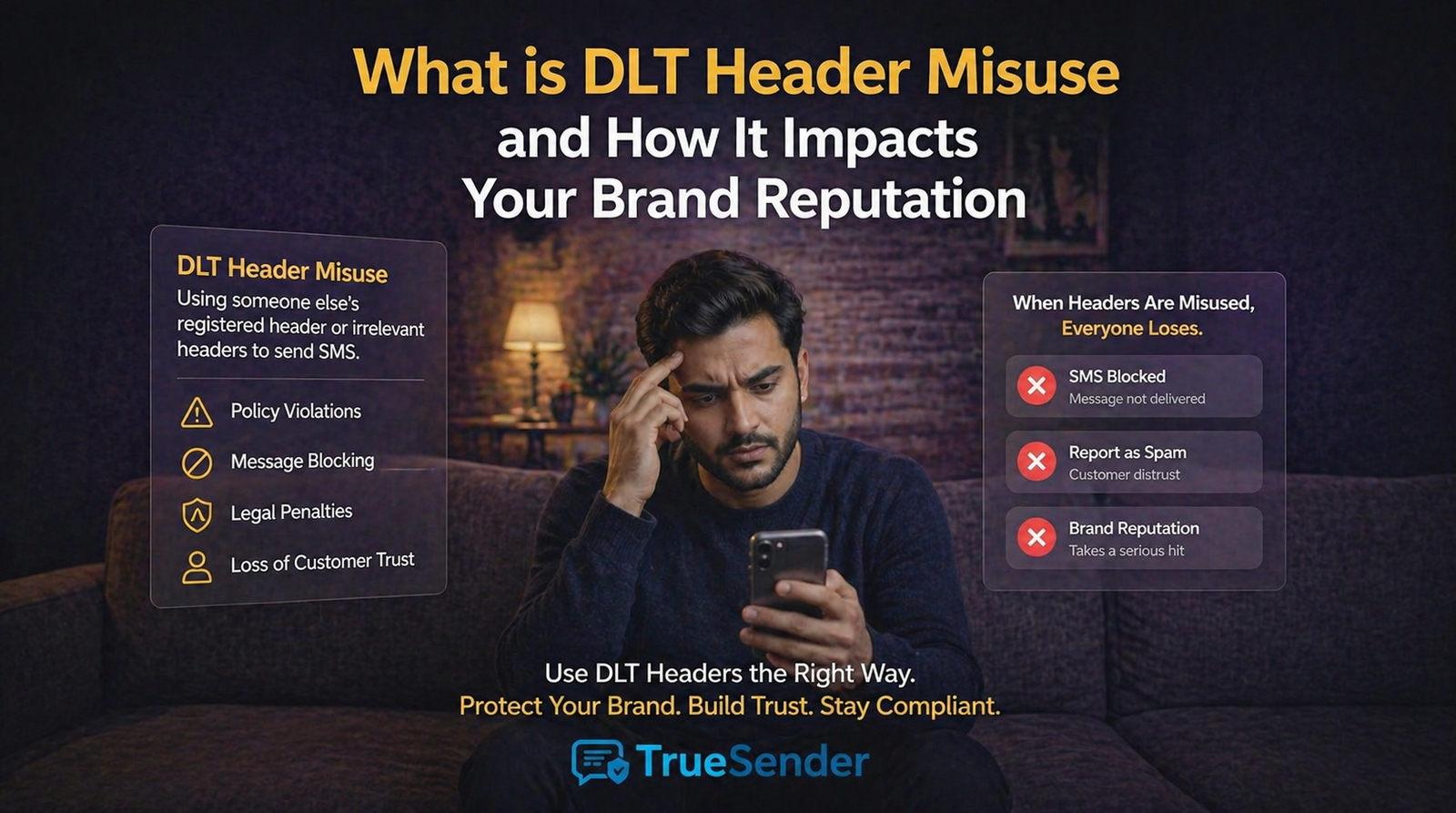
What is DLT Header Misuse?
DLT header misuse refers to the
unauthorized use of a registered SMS header (sender ID) by fraudsters to
impersonate a legitimate business.
In simple terms, a scammer sends messages using your company’s sender ID, making the SMS appear
genuine to recipients.
Example:
A customer receives a message from a trusted bank header like “HDFCBK”
asking for OTP or payment details.
Even though the header looks real, the message is fraudulent.
This is also known as:
- SMS header fraud
- Sender ID spoofing
- Brand spoofing in SMS
Why DLT Headers Matter in SMS Communication
DLT (Distributed Ledger Technology) was introduced by telecom regulators
(like TRAI in India) to:
- Ensure transparency in SMS communication
- Prevent spam and fraud
- Authenticate sender identities
Each business must register:
- Sender IDs (headers)
- Message templates
- Consent records
Despite these controls, loopholes and poor monitoring can still lead to
misuse.
How DLT Header Misuse Happens
Understanding how fraudsters exploit the system can help you prevent it.
Common methods used
in SMS header fraud:
- Phishing Campaigns
- Fraudsters send fake links using trusted headers
- Users unknowingly share sensitive data
- OTP Theft Attacks
- Messages trick users into sharing OTPs
- Leads to financial fraud
- Unauthorized API Access
- Weak API security allows misuse of registered headers
- Compromised Vendor Accounts
- Third-party SMS providers may get hacked or misused
- Template Manipulation
- Slight variations in templates bypass DLT filters
Impact of DLT Header Misuse on Your Brand
The damage caused by brand spoofing in SMS goes far beyond a
single fraudulent message.
1. Loss of Customer
Trust
Customers trust SMS messages from known headers.
Once they realize fraud is happening under your name, trust erodes quickly.
2. Financial Losses
- Customers may lose money due to scams
- Businesses may face compensation claims
3. Legal and
Compliance Risks
Regulators like TRAI impose strict penalties for:
- Spam violations
- Unauthorized messaging
- Data misuse
4. Brand Reputation
Damage
Negative experiences spread fast:
- Social media complaints
- Poor online reviews
- Loss of credibility
5. Reduced SMS
Engagement
Customers may start ignoring all messages from your brand, affecting:
- Campaign performance
- Conversion rates
Real-World Example of SMS Header Fraud
Imagine an e-commerce company running festive offers.
A fraudster sends this message:
“FLASH SALE! Get 90% OFF. Click here: fake-link.com”
The message uses the brand’s registered header. Customers click the
link, enter payment details, and lose money.
Even though the business is not directly responsible, customers blame
the brand.
How to Detect DLT Header Misuse
Early detection can prevent major damage.
Warning signs to
watch:
- Sudden spike in customer complaints
- Reports of suspicious SMS messages
- Unusual traffic patterns in SMS logs
- Messages sent outside approved templates
- Unknown API activity
Using tools like TrueSenderApp, businesses and users can identify
suspicious SMS patterns and flag potential fraud attempts in real time.
How to Prevent SMS Header Fraud (Step-by-Step)
Here’s a practical approach to safeguard your brand:
1. Secure Your SMS
APIs
- Use strong authentication (OAuth, API keys)
- Restrict IP access
- Monitor API usage regularly
2. Work with Trusted
DLT Providers
- Choose verified telecom partners
- Avoid low-cost, unverified SMS gateways
3. Strict Template
Governance
- Approve only necessary templates
- Regularly audit template usage
4. Monitor SMS
Activity in Real-Time
- Set alerts for unusual activity
- Track delivery and engagement metrics
5. Educate Your
Customers
- Inform users never to share OTPs
- Encourage reporting of suspicious messages
6. Use AI-Based
Protection Tools
Apps like TrueSenderApp help:
- Detect spam and phishing SMS
- Identify spoofed headers
- Protect user privacy with local processing
Best Practices to Protect Your Brand
To stay ahead of evolving threats, follow these best practices:
- Register all headers properly on DLT platforms
- Keep vendor access limited and monitored
- Regularly audit communication logs
- Implement multi-layer security for SMS systems
- Maintain transparency with customers
Why Businesses Must Take DLT Header Misuse Seriously
Ignoring DLT header misuse can have long-term consequences.
With increasing cases of SMS phishing scams and sender ID
spoofing, regulators are tightening rules and customers are becoming more
cautious.
Businesses that prioritize security:
- Build stronger customer trust
- Improve brand credibility
- Achieve better long-term engagement
Conclusion
DLT header misuse is not just a
technical issue - it’s a serious business risk. From financial fraud to brand
reputation damage, the consequences can be significant.
By understanding how SMS header fraud and brand spoofing in
SMS work, and by implementing strong preventive measures, businesses can
protect both their customers and their brand identity.
Tools like TrueSenderApp add an extra layer of protection,
helping detect and prevent fraudulent messages before they cause harm.
In a world where trust is everything, securing your SMS communication is
one of the smartest investments you can make.
